A Virtual Private Network (VPN) has become a critical tool for protecting online activity as privacy risks continue to grow. Many users browse the internet without realizing how much data gets collected, tracked, and stored during normal usage.
Personal information flows across multiple platforms, often without clear visibility or control. Continuous exposure like this increases the chance of misuse and unauthorized access.
Modern internet systems rely heavily on tracking technologies to monitor behavior and build detailed user profiles. Websites, advertisers, and service providers gather browsing patterns, search history, and interaction data to improve targeting accuracy.
Data leaks and security incidents can expose sensitive information without warning. A growing digital footprint makes privacy harder to maintain over time.
Public Wi-Fi networks introduce a serious security gap that many people overlook in daily situations. Open connections in cafés, airports, and hotels rarely provide strong encryption or protection against interception.
Attackers can monitor traffic, capture login details, and access personal accounts through weak network security. Convenience often comes at the cost of increased vulnerability.
A VPN helps reduce these risks by creating a secure and encrypted connection between a device and the internet. It protects identity, secures data transmission, and allows safer access across different networks.
According to Cloudflare, a Virtual Private Network creates an encrypted connection over a less secure network, helping protect user data and privacy. Strong encryption and routing through secure servers make online activity significantly harder to monitor.
What is a Virtual Private Network Definition
A Virtual Private Network (VPN) refers to a technology that establishes a secure connection between a device and the internet. Data moves through a protected channel instead of traveling across an exposed network path.
Sensitive information remains hidden from unauthorized access during transmission. Online activity gains stronger protection across different environments.
At a technical level, a VPN functions as an encrypted tunnel that secures data while it travels between endpoints. Information is encrypted before leaving the device and stays protected until it reaches the destination server.
Interception attempts fail to reveal readable content due to strong encryption standards. Security depends on how well the encryption and tunneling protocols are implemented.
The connection process begins when a user activates a VPN through an application installed on the device. The system connects to a remote server, which handles requests and forwards traffic to websites and online services.
The original IP address is replaced with the server identity, reducing the ability to trace user activity. Location and identity become less exposed during browsing sessions.
A Virtual Private Network is often compared to a proxy, yet both technologies operate at different levels of security. A proxy may redirect traffic without encrypting the entire connection, leaving certain data exposed.
VPNs secure all traffic passing through the connection and apply encryption consistently. The result provides stronger privacy protection and more reliable security for everyday use.
Key Features and Characteristics of a Virtual Private Network (VPN)
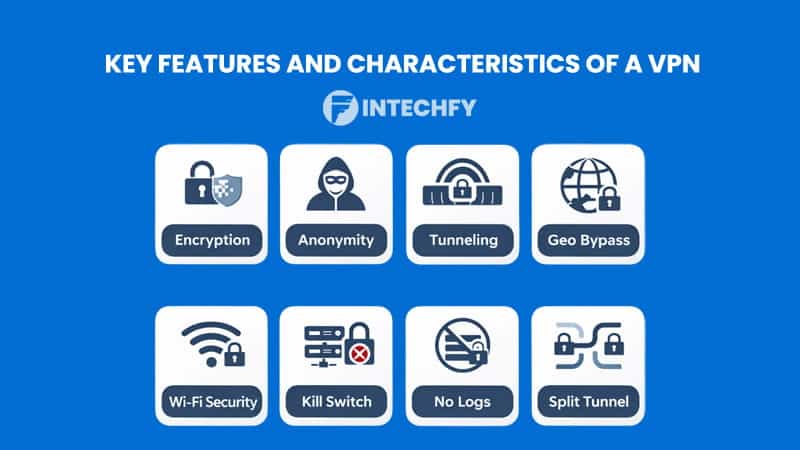
A Virtual Private Network offers a set of features designed to protect data, identity, and connection integrity during online activity. Each feature works together to reduce exposure across public and private networks. Security does not rely on a single layer but on a combination of mechanisms.
A strong configuration allows users to browse with more confidence and control.
Data Encryption & Confidentiality
A Virtual Private Network encrypts data before transmission, turning readable information into coded output. Hackers, ISPs, and network observers cannot interpret encrypted traffic without the correct keys. Strong encryption algorithms protect sensitive data such as passwords, messages, and financial details. Data confidentiality remains intact even across insecure networks.
Encryption also protects data integrity during transmission. Any attempt to modify packets becomes detectable during the process. This prevents tampering and ensures that information arrives unchanged. Secure communication depends heavily on consistent encryption strength.
IP Masking and Anonymity
A Virtual Private Network hides the original IP address and replaces it with a server-based identity. Online services detect the server location instead of the real user location. Tracking systems lose accuracy when IP data changes dynamically. This improves anonymity across websites and online platforms.
IP masking also reduces targeted profiling. Advertising systems rely on stable identifiers to track behavior patterns. A masked IP disrupts that tracking process. Privacy improves during everyday browsing sessions.
Secure Remote Access (Tunneling)
A Virtual Private Network creates a secure tunnel between the user device and a remote server. All traffic passes through an encrypted path before reaching the internet. Interception becomes significantly harder during transmission. Secure tunneling supports safe remote access for work and personal use.
Tunnel stability plays an important role in maintaining protection. Strong protocols ensure consistent encryption without data leaks. Reliable connections prevent exposure during network switching. Protection stays active across different environments.
Geo-Restriction Bypassing
A Virtual Private Network enables access to content restricted by geographic location. Connecting to servers in different countries changes the visible origin of traffic. Services respond based on server location rather than physical location. Access becomes more flexible across regions.
This capability supports streaming, research, and content access without regional limitations. Many platforms enforce restrictions due to licensing agreements. Server switching allows users to bypass those limits. Global content becomes easier to reach.
Public Wi-Fi Security
A Virtual Private Network protects data when using open and unsecured networks. Public Wi-Fi often lacks encryption, making traffic visible to attackers. Encrypted connections prevent data interception during transmission. Sensitive information remains protected in shared environments.
Risk levels increase when accessing accounts or financial services on public networks. Secure connections reduce exposure during these activities. VPN usage adds a necessary protection layer. Data security improves significantly in high-risk environments.
Kill Switch
A Virtual Private Network may include a kill switch that protects connections during unexpected drops. Internet access stops automatically if the VPN disconnects. Data does not leak through an unprotected connection. Privacy remains intact during unstable conditions.
Connection drops can occur due to network instability or server issues. Without a kill switch, traffic may continue without encryption. Real IP addresses could become visible. Automatic shutdown prevents accidental exposure.
No-Logging Policy
A Virtual Private Network provider may offer a no-logging policy that avoids storing user activity. Browsing history, connection timestamps, and IP records remain untracked. Reduced data storage lowers the risk of exposure or misuse. Privacy protection depends on provider transparency.
Different providers follow different policies regarding data retention. Users often review these policies before choosing a service. Strong privacy practices build trust. A strict no-log approach improves overall protection.
Split Tunneling
A Virtual Private Network can support split tunneling for flexible traffic management. Some data routes through the encrypted connection, while other traffic connects directly. This improves performance for selected applications. Users maintain control over how data flows.
Split tunneling supports scenarios where full encryption is not always required. Local services can run without routing through remote servers. At the same time, sensitive data remains protected. Balance between speed and security becomes easier to manage.
Core Components Behind VPN Technology

A Virtual Private Network relies on several core components that work together to secure data transmission. Each component handles a specific function, from encryption to authentication.
According to Cisco, VPN technology depends on tunneling, encryption, and authentication mechanisms to ensure secure communication across public networks. Strong integration between these elements ensures stable and secure connections.
Tunneling Protocols (The “Tunnel”)
Tunneling protocols define how data moves securely between endpoints. Each protocol offers different levels of speed, security, and compatibility. Choosing the right protocol affects performance and reliability. Modern VPN systems often support multiple protocols.
- WireGuard: Modern protocol designed for speed and simplicity. Lightweight structure allows faster connections with lower latency.
- OpenVPN: Open-source protocol known for flexibility and strong security. Widely used across different platforms and environments.
- IPsec (Internet Protocol Security):
Provides secure communication at the network level. Often used for enterprise connections. - L2TP/IPsec: Combines tunneling and encryption for added protection. Performance may be slower compared to newer protocols.
Encryption Engines (The “Privacy”)
Encryption engines handle how data gets secured during transmission. Strong algorithms prevent unauthorized access to sensitive information. Performance depends on how efficiently encryption runs on devices. Modern systems balance speed and security.
- AES-256 (Advanced Encryption Standard): High-level encryption used in government and enterprise systems. Known for strong resistance against attacks.
- ChaCha20-Poly1305: Efficient alternative designed for mobile devices. Performs well on lower-power hardware.
- Key Exchange (Diffie-Hellman): Enables secure key sharing between parties. Prevents interception during the setup phase.
VPN Clients (The “User Interface”)
A Virtual Private Network uses client applications to connect users to servers. These apps manage connection settings, protocol selection, and server switching. User interfaces simplify complex processes into accessible controls. Ease of use plays a major role in adoption.
Clients also handle automatic reconnection and security features. Background processes maintain stable connections without user intervention. Configuration options allow customization based on user needs. Reliable clients improve overall experience.
VPN Servers and Gateways (The “Endpoints”)
Servers and gateways act as connection points between users and the internet. They process requests, route traffic, and apply encryption. Infrastructure quality affects speed and reliability. Global server distribution improves accessibility.
- VPN Concentrators: Manage multiple VPN connections at once. Common in enterprise environments.
- Cloud Gateways: Provide scalable access through cloud-based infrastructure. Support flexible and global connectivity.
Authentication Systems (The “Security”)
Authentication systems verify user identity before allowing access to the network. Strong authentication prevents unauthorized entry. Multiple layers improve overall security. Identity verification remains a critical part of VPN systems.
- Multi-Factor Authentication (MFA): Adds an extra security layer beyond passwords. Combines different verification methods.
- Digital Certificates: Used to verify identity between devices and servers. Ensures trusted communication.
How a VPN Works to Secure Internet Connections
A Virtual Private Network secures internet connections through a structured process that protects data from the moment a connection begins. Each stage focuses on maintaining privacy, integrity, and anonymity during data transmission.
Multiple mechanisms operate together to prevent exposure across open networks. Strong coordination between these steps ensures a secure browsing experience.
| Step | Process | What Happens | Security Benefit |
|---|---|---|---|
| 1 | User Initiates Connection | User activates VPN and connects to a selected server | Ensures secure session setup and authentication |
| 2 | Secure Tunnel Creation | VPN creates an encrypted tunnel between device and server | Protects data from interception on public networks |
| 3 | Data Encryption | Data is encrypted before leaving the device | Keeps information unreadable to third parties |
| 4 | Traffic Routing | Internet traffic passes through the VPN server | Hides original source of the connection |
| 5 | IP Address Replacement | Real IP is replaced with VPN server IP | Enhances anonymity and prevents tracking |
| 6 | Data Decryption | Data is decrypted at the destination | Ensures safe and accurate data delivery |
User Initiates VPN Connection
A Virtual Private Network starts working when a user activates the service through an application. The client software connects to a selected server based on location or performance preference. Authentication may occur during this stage to verify user identity. Once connected, the system prepares to secure all outgoing and incoming traffic.
Connection initiation also allows users to select protocols and settings. Different configurations affect speed, security level, and compatibility. Automatic connection features can activate protection when joining new networks. Early setup plays a key role in overall connection security.
Secure Tunnel Creation
A Virtual Private Network creates an encrypted tunnel between the user device and the remote server. This tunnel acts as a protected pathway that shields data from external access. All transmitted packets travel through this secure channel instead of open network routes. Unauthorized interception becomes significantly more difficult.
Tunneling protocols define how the connection behaves under different conditions. Reliable protocols maintain stability during network changes. Strong tunnel integrity prevents leaks or exposure. Secure pathways remain active throughout the session.
Data Encryption Before Transmission
A Virtual Private Network encrypts data before it leaves the device. Plain text information becomes encoded using strong encryption algorithms. Intercepted data appears unreadable without the correct decryption key. Encryption ensures confidentiality during transmission.
Encryption strength depends on the algorithm and key management system. Modern protocols use advanced standards to maintain security without reducing performance. Secure encryption protects sensitive activities such as login sessions and financial transactions. Data remains protected across different network types.
Traffic Routing Through VPN Server
A Virtual Private Network routes all traffic through a remote server before reaching the internet. Websites and services interact with the server instead of the original device. This process hides the real source of the request. Routing adds an additional layer of privacy.
Server selection influences speed and latency. Closer servers often provide faster connections. Remote servers allow access to region-specific content. Traffic routing creates flexibility in how connections operate.
IP Address Replacement Process
A Virtual Private Network replaces the original IP address with the server’s IP identity. External systems detect the server location rather than the actual user location. Tracking systems lose accuracy when IP data changes. Anonymity improves during browsing.
IP replacement also reduces exposure to targeted monitoring. Many tracking tools depend on consistent IP identification. Changing IP addresses disrupts tracking patterns. Privacy becomes stronger across sessions.
Data Decryption at Destination
A Virtual Private Network decrypts data once it reaches the destination server or endpoint. Encrypted packets return to readable form for proper processing. Communication remains secure throughout the journey. Decryption completes the secure transmission cycle.
Secure decryption ensures that information arrives intact and usable. Any tampering attempts can be detected during processing. Data integrity remains preserved from origin to destination. The entire process maintains a secure loop of communication.
Types of Virtual Private Network (VPN)
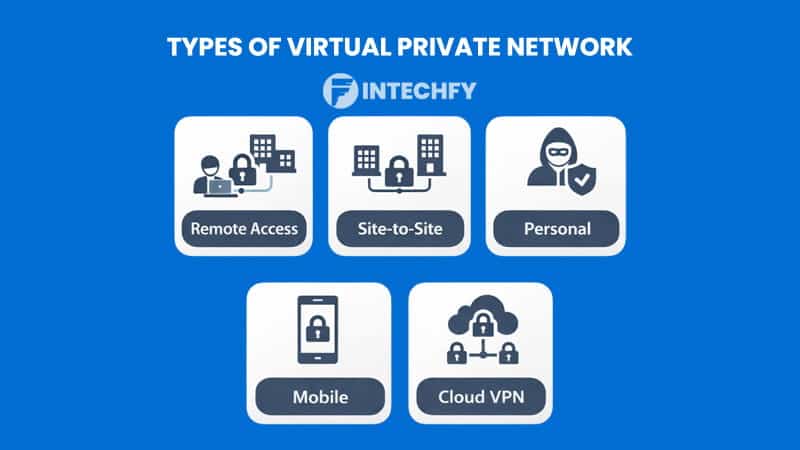
A Virtual Private Network can be implemented in several forms depending on user needs and network structure. Each type serves a specific purpose, from individual privacy to enterprise connectivity.
Different configurations offer flexibility in how connections are established. Selecting the right type depends on use case and environment.
Remote Access VPN
A Virtual Private Network designed for remote access allows individuals to connect securely to a private network from any location. Employees often use this setup to access company resources outside office environments. Encrypted connections protect sensitive data during remote work. Secure access becomes possible across different networks.
Site-to-Site VPN
A Virtual Private Network can connect multiple networks across different locations. Businesses use this setup to link branch offices with a central network. Data travels securely between sites without exposure to public networks. Communication between locations becomes seamless and protected.
Personal VPN
Personal VPN services focus on privacy and everyday browsing protection. Users connect to remote servers to hide IP addresses and secure traffic. These services are widely used for streaming, browsing, and avoiding tracking. Privacy improves across daily internet activity.
Mobile VPN
Mobile VPN solutions support devices that frequently switch between networks. Smartphones and tablets often move between Wi-Fi and mobile data connections. Stable connections ensure continuous protection without interruption. Mobility becomes easier without losing security.
Cloud-Based VPN
Cloud-based VPN systems operate through distributed server infrastructure. Users can connect to global servers without maintaining physical hardware. Scalability allows flexible expansion based on demand. Cloud integration supports modern remote environments.
Common VPN Topologies and Network Structures
A Virtual Private Network relies on different topologies and structures to organize how connections are established. Network design affects performance, scalability, and security.
Each topology serves a specific operational need. Proper design ensures efficient data flow across systems.
Common VPN Topologies
Different topologies define how devices and networks connect within a VPN system. Each model offers advantages depending on complexity and scale. Organizations choose structures based on communication needs and infrastructure design.
- Hub-and-Spoke (Remote Access/Branch Office): Central server manages all connections. Remote devices connect through a single hub.
- Full Mesh (Site-to-Site): Every node connects directly to all other nodes. High redundancy and reliability.
- Partial Mesh (Site-to-Site): Selected nodes connect directly. Balance between performance and complexity.
- Point-to-Point (PC-to-PC or Site-to-Site): Direct connection between two endpoints. Simple and efficient for limited use.
VPN Network Structures (Layers)
Network structures define how data operates across different layers within a VPN system. Each layer handles specific tasks related to routing and communication. Layer selection affects flexibility and performance.
- Layer 3 VPN (L3VPN / VPRN): Operates at the IP routing level. Supports scalable and flexible network design.
- Layer 2 VPN (L2VPN / VPLS): Provides connectivity similar to a local network. Devices behave as if connected within the same LAN.
- SSL VPN: Browser-based access without complex setup. Suitable for quick and secure remote connections.
Functions and Uses of VPN for Privacy and Security
A Virtual Private Network provides essential functions that protect data, identity, and communication across the internet. Strong security layers prevent unauthorized access during transmission.
Privacy features reduce exposure to tracking and monitoring systems. Reliable protection allows safer browsing across different environments.
Key Functions of a VPN
A Virtual Private Network operates through several core functions that work together to secure online activity. Each function focuses on protecting a different part of the connection.
Combined protection creates a stronger defense against cyber threats. These mechanisms form the foundation of secure internet usage.
- Data Encryption: A Virtual Private Network encrypts data before transmission, preventing interception by hackers or ISPs. Sensitive information such as passwords and messages stays protected during transfer.
- IP Masking & Privacy: A Virtual Private Network hides the real IP address and replaces it with a server identity. Online services detect the server location instead of the actual user location.
- Secure Tunneling: A Virtual Private Network creates an encrypted tunnel between the device and server. All traffic passes through this secure path, reducing exposure during transmission.
Common Uses for Privacy & Security
A Virtual Private Network supports a wide range of real-world use cases focused on privacy and security. Different scenarios require different levels of protection depending on the environment.
Flexible usage allows adaptation across personal and professional needs. Protection remains consistent across various network conditions.
- Public Wi-Fi Security: Encrypted connections protect sensitive data when using open networks. Login credentials remain safe in cafés or airports.
- Remote Work: Employees access company systems securely from outside office environments. Data remains protected across remote connections.
- Bypassing Censorship: Restricted websites become accessible through server switching. Users gain broader internet access across regions.
- Preventing Tracking: Tracking systems lose accuracy when IP addresses change. Online behavior becomes harder to profile.
- Avoiding Bandwidth Throttling: Encrypted traffic prevents ISPs from identifying usage patterns. Connection speed remains more stable during heavy usage.
Real-World Examples of VPN in Daily Use
A Virtual Private Network plays a practical role in everyday online activities. Real-world usage highlights how security and privacy features apply in different situations. Each scenario reflects a common need for safer connections. Daily tasks become more secure with proper protection.
Securing Public Wi-Fi
A traveler connects to airport Wi-Fi before boarding a flight. Encrypted traffic prevents interception of login details and personal data.
Accessing Geo-Blocked Content
A user connects to a server in another country to access region-locked streaming content. Content becomes available without changing physical location.
Remote Work Access
An employee logs into a company system from home using a secure connection. Sensitive business data remains protected during access.
Finding Cheaper Travel Deals
A user checks flight prices using different server locations. Price variations appear based on geographic location.
Securely Managing Finances
Online banking sessions run through encrypted connections. Financial data remains protected from potential interception.
Bypassing Censorship and Surveillance
Access to restricted websites becomes possible through remote servers. Users can browse freely in controlled environments.
Safe Downloading/File Sharing
File transfers occur through secure connections that protect data integrity. Downloaded content remains private during transmission.
Securing Online Gaming
Gamers connect through secure servers to reduce exposure to attacks. Stable connections improve overall gaming experience.
Avoiding Price Discrimination
Online stores display different prices based on location. Changing server regions helps identify fair pricing options.
Accessing Institutional Resources
Students connect to university systems from remote locations. Academic databases remain accessible and secure.
Advantages and Limitations of Virtual Private Network (VPN)
A Virtual Private Network offers clear benefits along with certain limitations that users should understand. Strong protection improves security and privacy across different scenarios.
At the same time, performance and compatibility may vary depending on usage. Balanced understanding helps users make better decisions.
Advantages of VPNs
A Virtual Private Network provides several advantages that improve online security and accessibility. Each benefit supports a specific aspect of internet usage. Combined advantages create a safer browsing environment. Protection extends across different platforms and devices.
- Enhanced Security: Strong encryption protects sensitive data from interception. Secure communication reduces exposure to cyber threats.
- Improved Privacy: IP masking hides user identity during online activity. Tracking systems become less effective.
- Geo-Block Bypass: Access to global content becomes possible through server switching. Regional restrictions no longer limit availability.
- Safe Remote Access: Secure connections allow access to private networks from any location. Work and personal data remain protected.
- Bypassing Censorship: Restricted content becomes accessible through secure routing. Internet access becomes more open.
Limitations of VPNs
A Virtual Private Network also comes with certain limitations that affect performance and usability. Understanding these factors helps avoid unrealistic expectations. Some trade-offs exist between security and speed.
Users should consider these aspects before choosing a service.
- Reduced Internet Speed: Encryption processes may slow down connection speeds. Performance depends on server distance and protocol.
- Costs: Premium services require subscription fees. Free options may offer limited features.
- Incompatibility: Some platforms block VPN connections. Access may be restricted on certain services.
- Free VPN Risks: Some free providers collect user data or show ads. Security standards may not match paid services.
- Not a Complete Security Solution: VPNs do not replace antivirus or firewall protection. Additional security tools remain necessary.
Differences Between VPN and Other Types of Computer Networks
A Virtual Private Network differs from traditional computer network types in how connections are established and managed. Most networks rely on physical infrastructure or fixed coverage areas. VPN technology operates as an overlay that runs on top of existing networks. This approach allows flexible and secure communication without requiring dedicated physical connections.
Traditional computer networks focus on location-based connectivity. VPNs focus on securing data regardless of location or network type. Users can connect across different environments without exposing sensitive information. The distinction lies in function rather than physical structure.
- PAN (Personal Area Network): Small-scale network connecting personal devices such as smartphones and laptops. Limited range and usually based on Bluetooth or direct connections.
- LAN (Local Area Network): Covers a specific area such as a home, office, or building. Devices connect through wired or wireless infrastructure.
- WLAN (Wireless Local Area Network): A wireless version of LAN that uses Wi-Fi technology. Common in homes, offices, and public hotspots.
- MAN (Metropolitan Area Network): Covers a city or large urban area. Connects multiple LANs within a region.
- WAN (Wide Area Network): Spans large geographic areas such as countries or continents. The internet itself is the largest example.
- CAN (Campus Area Network): Connects multiple buildings within a campus or organization. Common in universities and corporate environments.
- SAN (Storage Area Network): Dedicated network for high-speed data storage and retrieval. Used in enterprise environments for managing large data volumes.
A Virtual Private Network stands apart from these models by acting as a secure layer on top of any existing network. It does not replace infrastructure but enhances security through encryption and routing. This structure allows users to operate across different networks while maintaining privacy.
Conclusion
A Virtual Private Network plays a vital role in protecting online activity across modern digital environments. Strong encryption, IP masking, and secure tunneling work together to reduce exposure to tracking and cyber threats.
These features allow users to maintain privacy even on unsecured networks. Reliable protection has become increasingly important as data usage continues to grow.
Online activity now involves constant interaction with platforms that collect and analyze user data. Without proper protection, sensitive information can be exposed or misused.
VPN technology offers a practical solution for maintaining control over digital identity. Secure connections support safer browsing, communication, and remote access.
A Virtual Private Network remains highly relevant in everyday use, from personal browsing to professional work environments. Flexible deployment allows users to adapt security based on different needs.
Continued growth in digital services increases the importance of secure connections. Privacy protection is no longer optional but a necessary part of online activity.
FAQs About Virtual Private Network
Is using a VPN safe?
Yes, safety depends on using a trusted provider with strong encryption and a clear privacy policy.
Is VPN a type of WiFi?
No, VPN is a security technology that works on top of existing networks, including Wi-Fi.
Can you tell if someone is using a VPN on your Wi-Fi?
Detection is sometimes possible through traffic patterns or unusual routing behavior.
Can a VPN be detected?
Certain platforms can identify VPN usage based on IP databases or traffic analysis.
How to access a virtual private network?
Access usually involves installing a VPN app, logging in, and connecting to a server.